New KCodes NetUSB Bug Affect Millions of Routers from Different Vendors

Cybersecurity researchers have detailed a high severity flaw in KCodes NetUSB component that’s integrated into millions of end-user router devices from Netgear, TP-Link, Tenda, EDiMAX, D-Link, and Western Digital, among others.
KCodes NetUSB is a Linux kernel module that enables devices on a local network to provide USB-based services over IP. Printers, external hard drives, and flash drives plugged into a Linux-based embedded system (e.g., a router) are made available via the network using the driver.
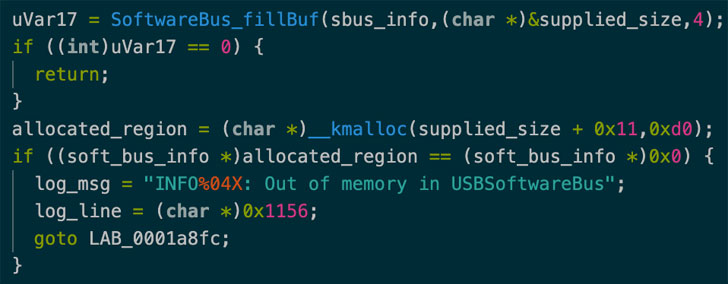
CVE-2021-45608 (CVSS score: 9.8), as the security flaw is tracked as, relates to a buffer overflow vulnerability that, if successfully exploited, can allow attackers to execute code remotely in the kernel and perform malicious activities of their choice, according to a report shared by SentinelOne with The Hacker News.
This is the latest in a string of NetUSB vulnerabilities that has been patched in recent years. In May 2015, researchers from SEC Consult disclosed another buffer overflow flaw (CVE-2015-3036) that could result in a denial-of-service (DoS) or code execution.
Then in June 2019, Cisco Talos divulged details of two weaknesses in NetUSB (CVE-2019-5016 and CVE-2019-5017) that could allow an attacker to inappropriately force select Netgear wireless routers into disclosing sensitive information and even giving the attacker the ability to remotely execute code.
Following responsible disclosure to KCodes on September 20, 2021, the Taiwanese company issued a patch to all vendors on November 19, after which Netgear released firmware updates containing fixes for the vulnerability.
SentinelOne has refrained from releasing a proof-of-concept (PoC) code in light of the fact that other vendors are still in the process of shipping updates. But the cybersecurity firm cautioned the possibility of an exploit emerging in the wild despite the technical complexity involved, making it imperative that users apply the fixes to mitigate any potential risk.
“Since this vulnerability is within a third-party component licensed to various router vendors, the only way to fix this is to update the firmware of your router, if an update is available,” researcher Max Van Amerongen said. “It is important to check that your router is not an end-of-life model as it is unlikely to receive an update for this vulnerability.”